Access Control and Authentication Patterns for LLM Services: A Security Guide

- Mark Chomiczewski
- 12 May 2026
- 0 Comments
Building a Large Language Model (LLM) service feels like handing the keys to your entire database over to a very smart, but occasionally hallucinating, intern. The excitement of deploying AI often outpaces the security planning, leaving organizations exposed to unauthorized access, data leaks, and malicious manipulation. You aren't just securing an API endpoint anymore; you are protecting a dynamic reasoning engine that can be tricked into bypassing its own rules.
The core problem isn't just keeping bad actors out-it's ensuring that legitimate users and automated agents only do exactly what they are supposed to do, nothing more. Traditional security models struggle here because LLMs introduce unique attack vectors like prompt injection and complex agent interactions that standard firewalls don't understand. This guide breaks down the specific access control and authentication patterns you need to implement right now to secure your LLM services effectively.
Why Traditional Access Control Fails with LLMs
You might think your existing Role-Based Access Control (RBAC) system is enough. It’s not. In traditional software, permissions are static. A user has a role, and that role grants access to specific functions. With LLMs, the context changes with every request. An LLM doesn’t just execute a command; it interprets intent. If you don’t have granular controls, a user with "read-only" access could potentially craft a prompt that tricks the model into revealing sensitive training data or executing administrative actions through social engineering.
Consider the "black box" nature of neural networks. When a decision is made by a model, tracing exactly why it granted or denied access is difficult. This lack of transparency creates audit nightmares for compliance-driven industries like healthcare or finance. According to research from OpenIdentity Platform, while standard RBAC remains transparent for auditing, it lacks the contextual awareness needed for dynamic LLM environments. They found that neural network-based authorization decisions achieved 22% higher accuracy in detecting sophisticated threats but suffered from nearly impossible auditability due to the sheer volume of intermediate computations.
This means you can’t rely on a single method. You need a hybrid approach that combines the clarity of traditional roles with the adaptability of modern, attribute-based systems. Ignoring this distinction leaves you vulnerable to subtle exploits where the model itself becomes the backdoor.
Core Authentication Mechanisms for LLM Services
Authentication is the first line of defense. For LLM services, you need mechanisms that are both secure and stateless, as these platforms often handle high volumes of concurrent requests. The industry standard has shifted toward OpenID Connect (OIDC) and OAuth2 standards. These protocols allow you to identify and authenticate all principals-including humans and autonomous agents-without exposing raw credentials.
Avoid using simple API keys for sensitive LLM interactions if possible. API keys are static secrets that, once leaked, remain compromised until rotated. Instead, use JSON Web Tokens (JWT). JWT-based session tokens are the preferred choice for secure, stateless authentication in LLM platforms. As demonstrated by DreamFactory’s implementation, these tokens can be easily validated or revoked as needed, providing a layer of security that adapts to real-time risk assessments.
- Stateless Validation: JWTs carry their own claims, allowing the server to verify authenticity without checking a central database, reducing latency.
- Short Lifespans: Issue tokens with short expiration times (e.g., 15 minutes) to limit the window of opportunity if a token is stolen.
- Revocation Lists: Maintain a lightweight blocklist for immediate invalidation of compromised sessions.
Performance matters here too. Benchmarks from Curity’s 2024 MCP Authorization study indicate that properly implemented LLM access controls add only 15-45ms latency to API calls. Stateless JWT validation performs 38% faster than session-based alternatives, making it the efficient choice for high-throughput AI applications.
Authorization Strategies: RBAC vs. ABAC vs. PBAC
Once a user or agent is authenticated, you must decide what they can do. This is where authorization comes in. While RBAC is familiar, it’s too rigid for the nuanced world of AI. Attribute-Based Access Control (ABAC) and Policy-Based Access Control (PBAC) are becoming the gold standards for LLM security.
| Model | Best For | Granularity | Auditability | Complexity |
|---|---|---|---|---|
| RBAC | Human users with fixed roles | Low (Role-based) | High | Low |
| ABAC | Dynamic contexts (time, location) | Medium (Attribute-based) | Medium | Medium |
| PBAC | Enterprise policy enforcement | High (Policy-driven) | Variable | High |
Calypso AI’s 2024 research emphasizes that permissioning models must be prioritized to mitigate risk. PBAC enables only identified personnel to engage with the model based on company policy, business need, or other enterprise-specific determinants. For example, a policy might state: "Allow access to financial data only if the user is in the Finance department AND accessing from a corporate IP address AND during business hours."
This level of detail is crucial for preventing misuse. Adrian Machado, CTO of DreamFactory, recommends defining specific roles like "LLM Administrator" with full access and "Data Analyst" with read-only permissions to ensure permissions are tightly aligned with each user's responsibilities. However, he also notes that RBAC simplifies API permission management, so many teams start there and layer ABAC rules on top for edge cases.
Securing AI Agents and Automated Workflows
One of the most overlooked areas in LLM security is the authentication of AI agents themselves. Your LLM might act as an agent that interacts with other APIs, databases, or services on behalf of a user. How does this agent prove its identity?
WorkOS’ 2024 comparison of authentication patterns for AI agents identified three primary credential handling approaches:
- Direct Injection: Used in 63% of early implementations but rated "high risk" due to the potential for credential leakage in logs or prompts.
- Secret Storage Services: Adopted by 28% of enterprises using tools like AWS Secrets Manager. This keeps credentials isolated and encrypted.
- OAuth Delegation: Growing at 47% year-over-year as the preferred enterprise solution. The agent acts on behalf of the user, inheriting their permissions rather than having its own broad privileges.
Handling Multi-Factor Authentication (MFA) for AI agents is particularly tricky. OpenAI’s Computer Use API and Anthropic’s equivalent typically prompt users to manually provide one-time passcodes so the LLM never sees the secret factor. This creates workflow disruptions reported by 72% of early adopters. To solve this, consider implementing headless MFA flows or using hardware-backed keys that can be verified programmatically without human intervention.
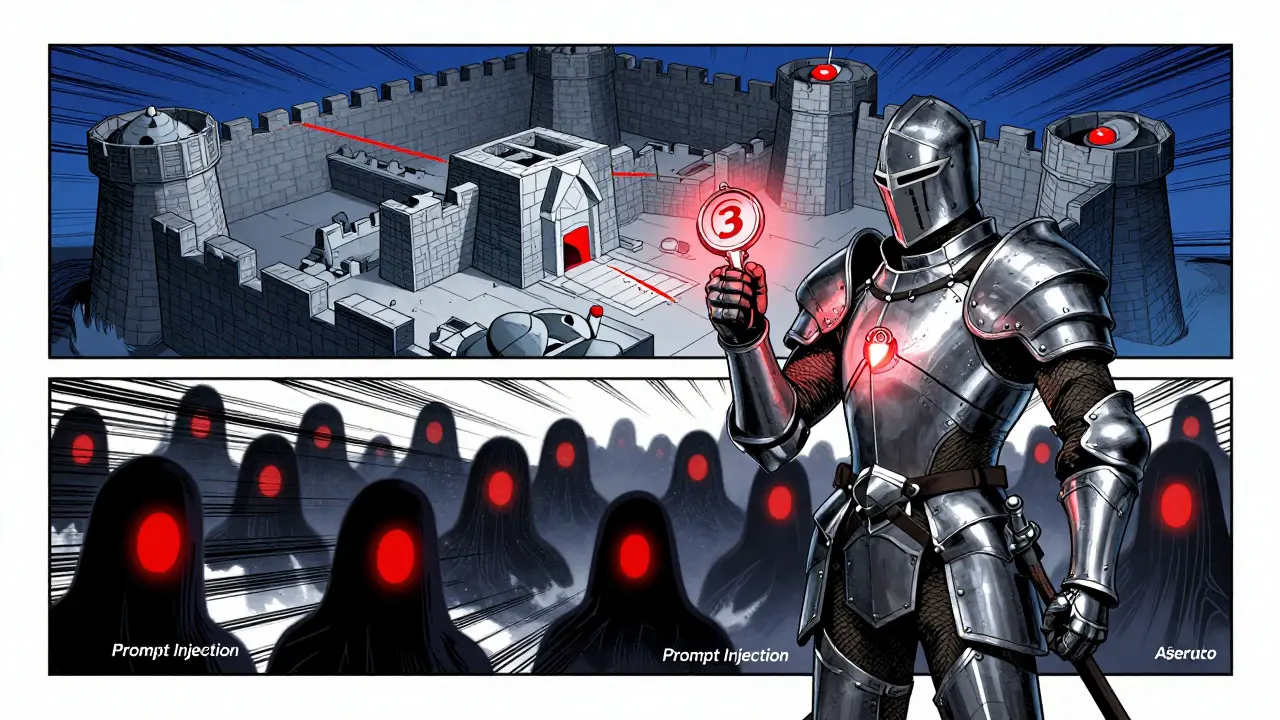
Mitigating Prompt Injection and Input Risks
Even with perfect authentication and authorization, your LLM service is vulnerable to prompt injection. This is where a user crafts input designed to override the system’s instructions. Security researcher Jane Chen of Witness AI cautions that prompt injection remains the most prevalent LLM security threat, noting their 2024 analysis found 83% of tested commercial LLM implementations vulnerable without proper input sanitization.
To combat this, you need mandatory input validation layers before the prompt reaches the model. This includes:
- Semantic Filtering: Using a secondary, smaller model to analyze the intent of the user’s prompt before passing it to the main LLM.
- Context Separation: Clearly distinguishing between system instructions and user input within the prompt structure to prevent confusion.
- Rate Limiting: Implement strict rate limits, typically 5-50 requests per minute per user, to slow down automated attacks.
Beyond Identity’s research shows that organizations implementing AI-enhanced authentication achieve 37% fewer account takeover incidents. By combining behavioral biometrics-such as typing patterns and mouse movements-with traditional checks, you can detect anomalies that suggest a human is being coerced or an automated script is taking over.
Implementation Challenges and Best Practices
Implementing these patterns isn’t trivial. Enterprises typically require 8-12 weeks for initial implementation of comprehensive LLM security frameworks, with 65% of organizations underestimating the required effort by at least 30%. Common pain points include configuring OAuth scopes for LLM agents and managing the complexity of ABAC rules.
Reddit discussions in r/cybersecurity reveal common struggles, with one admin reporting spending three weeks configuring OAuth scopes before realizing they needed ABAC rules for time-based restrictions. Documentation quality varies significantly; newer PBAC frameworks often suffer from incomplete documentation covering only 63% of edge cases, according to 2024 developer surveys.
To succeed, follow these best practices:
- Start with Zero Trust: Assume every request is malicious until proven otherwise. Verify explicitly, grant least privilege, and assume breach.
- Use Hybrid Auditing: Since neural network decisions are hard to audit, log all inputs, outputs, and metadata separately. Use simple machine learning algorithms to flag suspicious events for human review.
- Train Your Team: 89% of job postings for "LLM Security Specialists" require both CISSP certification and practical experience with prompt injection mitigation. Invest in upskilling your existing security team.
- Monitor Continuously: Security is not a one-time setup. Monitor for unusual access patterns, such as a user accessing production data outside business hours, which Beyond Identity’s case studies show can be detected via simple queries.
The market is moving fast. Gartner projects the LLM security market will reach $4.7 billion by 2026, growing at a 68% CAGR. Regulatory bodies like NIST are already updating frameworks, with the AI Risk Management Framework (AIRMF) 1.1 update explicitly requiring transparent access control mechanisms for high-impact AI systems. Don’t wait for compliance deadlines to force your hand. Build robust access control and authentication patterns now to protect your data, your users, and your reputation.
What is the best authentication method for LLM services?
The best authentication method for LLM services is OpenID Connect (OIDC) combined with JSON Web Tokens (JWT). This provides stateless, secure, and easily revocable session management that scales well with high-volume API calls.
How do I prevent prompt injection attacks?
Prevent prompt injection by implementing mandatory input validation, semantic filtering using a secondary model, and clear separation between system instructions and user input. Additionally, enforce strict rate limiting to slow down automated attacks.
Is RBAC sufficient for securing AI agents?
No, RBAC is generally insufficient for AI agents due to its static nature. Attribute-Based Access Control (ABAC) or Policy-Based Access Control (PBAC) is recommended to handle dynamic contexts and fine-grained permissions required for autonomous agents.
What are the biggest security risks for LLM deployments?
The biggest risks include prompt injection, unauthorized data access, credential leakage in agent workflows, and the lack of auditability in neural network decision-making processes.
How long does it take to implement LLM security frameworks?
Enterprises typically require 8-12 weeks for initial implementation of comprehensive LLM security frameworks. Many organizations underestimate the effort by at least 30%, so planning for additional time and resources is advisable.